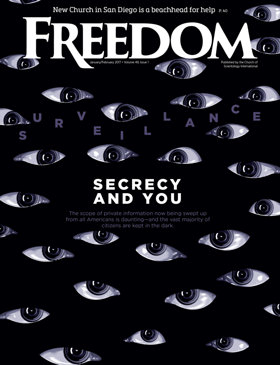
When most of us think about government surveillance, we tend to have an image of someone watching us on camera, reading our emails as they’re typed or listening to our phone conversations. The idea of “surveillance after the fact” usually doesn’t cross our minds.
As an associate professor of communications at the University of Utah in Salt Lake City, Sean Lawson spends quite a bit of time pondering the concept. After all, he lives and works just 25 miles from the Utah Data Center, a sprawling National Security Agency (NSA) campus that epitomizes retroactive surveillance.

Located near a National Guard training site in the Salt Lake Valley town of Bluffdale, the NSA facility boasts one of the largest arrays of computer servers anywhere for storing metadata on every phone call, text message, email and social media interaction since the September 11, 2001, terrorist attacks on America.
“You might not be of interest to the government right now, but in the future maybe you will be,” says Lawson, who majored in Arab Studies at Georgetown University and studies the effects of science and technology on military doctrines and strategies. “Maybe you’ll be accused of a crime or you’ll come into the government’s focus for some other reason, such as political activism.”
As Lawson sees it, the danger of the NSA’s penetrating, all-pervasive surveillance of citizens lies in the fact that the agency has an archive of everybody’s life—everything they’ve ever done electronically, down to the details of their grocery purchases. All of it, Lawson worries, can be mined by the government in an ostensible effort to fight terrorism.
“The idea of the government collecting and storing massive amounts of information about people does rub up against the core principles and values that this country was founded on,” says Lawson. “But just from a practical standpoint, I wonder how effective all the data collection really is and if it’s even necessary.”
Lawson points to the conclusions of two independent commissions on NSA reform, including one by a 2013 White House review group, which found that not only was the agency’s collection of telephone metadata in violation of the law (and potentially also of the Constitution), but also that the program has never made any impact on countering terrorism.
“The idea of the government collecting and storing massive amounts of information about people does rub up against the core principles and values that this country was founded on.”
Lawson’s interest in the potentially negative impact of government policy goes back to his boyhood in California’s San Francisco Bay Area. It was there that he first learned about the destructive power of nuclear weapons, not least because his father worked on the U.S. nuclear weapons program at the nearby Lawrence Livermore National Laboratory. Dinner-table conversations at the Lawson home frequently revolved around the profound impact of technology on human conflict.
“That sparked in me an interest in the implications of other kinds of technologies and weapons,” says Lawson, who is the author of Nonlinear Science and Warfare: Chaos, Complexity and the U.S. Military in the Information Age, a 2013 book recently translated into Chinese.
A small but significant movement in the intelligence world has been pushing for some years now for greater amounts of human intelligence rather than the electronic collection of massive amounts of data, according to Lawson. “I don’t think we need to go back to a romanticized world of covert agents like James Bond,” he says. “But there is some merit to the idea that we’re maybe too enamored of technology.”
One of the problems with the NSA is that “on the one hand they’re the organization that has the most expertise on cybersecurity issues,” Lawson says. “But on the other hand they have an organizational mission that works against cybersecurity because their mission is espionage—to break into communications systems and spy on other people.”
So, Lawson explains, to some extent the NSA has a vested interest in not promoting cybersecurity. That way the agency can continue to use vulnerabilities in cybertechnology to promote its main mission.
Because cyberattackers (the bad guys) and cyberdefenders (the good guys, including everyday consumers and companies) use the same information technology, there has long been a fundamental tension between cyberattacks and cyberdefense.
The NSA refers to this as the “equities issue”—when the agency discovers a vulnerability in a technology or system, it has two options: The first is to alert the manufacturer (or private-sector consumer) and help fix the vulnerability, thereby protecting both cyberdefenders and cyberattackers. The other option is to keep quiet in the hope of catching the bad guys, but also leaving the good guys insecure.
As Lawson puts it: “The NSA doesn’t necessarily let private companies know in a timely manner that their products have vulnerabilities because the NSA wants to exploit them for espionage purposes.”
The Cybersecurity Information Sharing Act of 2015 requires the Director of National Intelligence, who oversees the NSA, to develop procedures to share cybersecurity threat information with private entities—unless the information is deemed too valuable to disclose in the interests of national security.
But there’s the rub: It is unclear “how big the space is for exceptions,” says Lawson.