

 ally, new to the executive level at her company, is on a business trip. It is late at night when she arrives at her hotel. A frequent credit card user, she tries to check in with a Visa card. But the card is over her credit limit and the hotel won’t accept it. Bewildered, she tries Mastercard, then another — all to no avail. She is stranded in a hotel which will not check her in.
ally, new to the executive level at her company, is on a business trip. It is late at night when she arrives at her hotel. A frequent credit card user, she tries to check in with a Visa card. But the card is over her credit limit and the hotel won’t accept it. Bewildered, she tries Mastercard, then another — all to no avail. She is stranded in a hotel which will not check her in.
She later learns that her credit cards had been “banged” by hackers who obtained her card numbers through the Internet.
When finally tracked down, the ringleader, known as “Agent Steal,” claims it was a simple prank — “my own kind of freedom of expression.”
A freak aberration in the world of the Internet? Unfortunately not.
Take Robert, a software development programmer in Santa Monica, California. Working from his home, he makes his living producing programs for business applications.
One morning he sits down to put the finishing touches on a new program which should save office accountants hours of time each week.
But when he logs on, he finds “black flags” — small but unmistakable signs that his computer has been electronically broken into. He is frantic but has no viable way of finding out what has happened, nor the consequences.
A piece of anonymous e-mail tells the story: a skilled hacker broke into his computer — which was linked to the Internet — and posted his newly completed program onto a “freeware” computer bulletin board, where users can “visit” and download software programs free of charge.
The effect is obvious: months of work — work which he was doing to earn his next paycheck — may just as well have never happened. Adding further insult to injury, the hacker announces that he will send the program to other freeware boards across the world.
Robert responds and asks the hacker why he did what he did — had the hacker somehow been wronged or offended by him? Does he profit from purloined programs?
"No,” the hacker responds to both inquiries. He says that Robert’s problem is that he is one of the “elite” who does not recognize that inherently “all information wants to be free.” And, finally, the hacker explains that disseminating software programs is just his exercise of his “freedom of speech.”
These true stories — the victims requested their names be withheld to avoid provoking further hacker attacks — illustrate a gathering storm in cyberspace. Ultimately, even beyond the break-in and piracy epidemic — estimates are that as much as 50 percent of the software in use today is stolen or pirated — the “freedom of speech” excuse for these acts and a legion of others is the greatest threat.

It is also a bogus excuse for a crime but the judiciary should be on the front lines of differentiating between theft and valid free speech matters. But many courts of law are willing to turn a blind eye or to let misplaced concern over possible “chilling” of the First Amendment — even when the First Amendment is no part of the matter — justify letting criminal acts go unpunished.
Case in point:
David LaMacchia of Boston operated an electronic bulletin board from Massachusetts Institute of Technology and encouraged users from around the world to copy more than $1 million in software purloined from Microsoft, Excel and other software producers.
The losses to software producers and distributors were enormous, irreparable and continuing. LaMacchia’s acts effectively destroyed the value of scores of programs.
With LaMacchia facing criminal charges, his lawyer argued that his client’s conduct could in no wise be deemed criminal as he did not profit personally from scattering the costly computer programs free of charge.
But he also argued that the First Amendment permitted — even encouraged — this criminal conduct. LaMacchia effectively argued that, under the First Amendment, ownership and property were meaningless concepts.
LaMacchia beat the charges and the case was dismissed.
The judge on the case, U.S. District Judge Richard G. Stearns, expressed disapproval of LaMacchia’s conduct, but complained that his hands were tied by a lack of existing laws. “If the indictment is to be believed, one might at best describe LaMacchia’s actions as irresponsible, and at worst as nihilistic, self-indulgent, and lacking in any fundamental sense of values,” he said. But he stopped short of calling it what it truly was: a criminal act committed with constitutional air-cover.
Whether viewed as a case of judicial weakness or prosecutorial failure, LaMacchia’s case stands as an ominous precedent.
With this logic, a thief could rob a bank, give the stolen money to others, claim his theft was his “statement” against the bank and thus sheltered by the First Amendment, and gain acquittal.
Robert Kruger, director of enforcement for Business Software Alliance, a Washington, D.C.-based group representing major software makers, and a former federal prosecutor, says, “It is just flat-out theft. You are taking someone’s hard work and reproducing it without compensation.”
And in some cases, the courts are willing to recognize this fact. In March 1995, the same federal court sentenced Richard Kenadek, who committed nearly identical acts, to two years’ probation and ordered him to forfeit all equipment related to his bulletin board service. Kenadek, like LaMacchia, made software available on his bulletin board service, but unlike LaMacchia, he charged fees to users — and raised no “First Amendment” defense.
Winn Schwartau, author of Information Warfare, analyzed the effects of such conduct on the business world: “If you invest five years and $1 billion in a new invention, either a product or process, you hope to make a profit on that investment. If, however, I can steal the knowledge to make that product, say for $10 million, I can sell the same item for substantially less and bring it to market in months instead of years. You invest the time and the money, I steal the results, then we compete. Who’s got the advantage?”
Lack of personal restraint by some computer users and lack of effective legal restraint has led to runaway abuse. “For every one computer break-in you become aware of, there are another 399 break-ins you don’t know about” said Schwartau.
Attorney and author Lance Rose supports strong law enforcement action against infringers. “They’re doing their job in reminding corporate America that just because it’s easy to copy doesn’t mean it’s legal”, he said.

The problems reach far beyond the private sector. Many break-ins affect national security.
In Toulon, France, a U.S. Naval base maintained computerized records of “submarine signatures” — the unique sounds transmitted by American subs to distinguish them from others, but recognizable only by those who hold this classified information. In October 1995, the computer that stored these was electronically broken into and the information stolen.
At the Pentagon, no less than 250 attempted computerized break-ins occur per day. Freedom found six electronic bulletin board services on the Internet that contained statements that the posters had illicitly obtained classified information from top security sources in the U.S. government.
It was no surprise to read one poster’s statement that “... this is America, and I am free to express myself by sending this information to those who have an interest.”

A growing number in the private sector have awakened to the need for reforms.
The Center on Speech, Equality and Harm, which operates a site on free speech on the World Wide Web, feels that the concept of “free speech” has been sorely abused, pointing to how laws regulate many categories of expression to prevent harm or to encourage equality. These include speech used to form a criminal conspiracy or to defame or libel, violate a trademark or copyright, or defraud a consumer. Laura Lederer, Executive Director of the Center, told Freedom, “The issue is, does the speech harm and if it does, what can be done about it?”
She also rejected the idea of an Internet free of the regulations which apply to everyday life. “If the Net is being used for illegal activities, people need to cooperate with the government to eradicate that” Lederer said. “They’re playing directly into this illegality when they say it should be completely free.” John Powell, law professor at the University of Minnesota and former legal director of the American Civil Liberties Union, agrees. “There’s a lot of confusion. You can use speech for violence. You can use speech to deny someone freedom of expression” he told Freedom.
On the Internet, this expresses itself in such concepts as “no one is responsible” and “nobody really owns anything” which deny accountability for the basic tenets of property ownership and wind up costing American consumers billions each year. (See “The Open Door to Piracy” page 4.)

Internet and computer crimes are all over the newspapers and airwaves — except for those crimes committed in the name of “free speech.” No matter how spurious the claim, some reporters and editors buy the rationale — because it fits their own needs and motives.
Unscrupulous media outlets contribute to the problem of subversion of intellectual property when it comes to trade secrets — which the Uniform Trade Secrets Act defines as “information, including a formula, pattern, compilation, program, device, method, technique or process, that: (1) derives independent economic value, actual or potential, from not being generally known to the public or to other persons who can obtain economic value from its disclosure or use; and (2) is the subject of efforts that are reasonable under the circumstances to maintain its secrecy.”
When was the last time the formula for Coca-Cola ran in the morning paper? If it ever were published, the legal thunderclap from a company as powerful as Coca-Cola would be deafening. The right to maintain such secrets is guaranteed under Article I of the Constitution and has been upheld in courts throughout the country.
 Yet it seems to be open season on trade secrets,Copyrights and other proprietary information, which seem to become “fair game” in the media world when it suits the needs of some editors and reporters. In an ongoing case, the Church of Scientology was forced to file suit against the Washington Post after attempts to resolve the matter informally failed and the Post unlawfully published some of the Church’s sacred and confidential religious scriptures — scriptures which are also subject to legal protection under copyright and trade secret law.
Yet it seems to be open season on trade secrets,Copyrights and other proprietary information, which seem to become “fair game” in the media world when it suits the needs of some editors and reporters. In an ongoing case, the Church of Scientology was forced to file suit against the Washington Post after attempts to resolve the matter informally failed and the Post unlawfully published some of the Church’s sacred and confidential religious scriptures — scriptures which are also subject to legal protection under copyright and trade secret law.
But when the Church sought to enjoin the improper use of these materials and to have them returned, the newspaper justified its wrongdoing by claiming it had simply exercised its First Amendment right.
The same claims were made when the Church filed suit against the individuals who unlawfully provided the materials to the Post and attempted to disseminate them to others through the Internet. The Church endeavored to enjoin these postings and to recover the scriptures themselves.
Putting the matter in the context of a secular creation further clarifies the issue: An individual steals from a songwriter the lyrics to an unpublished song and sends them out on the Internet. When the law catches up to the thief, he defends himself by claiming it is all a case of free speech. The songwriter, in other words, is attempting to “silence” the thief’s First Amendment rights. In reality, the songwriter is seeking to protect his creative work and safeguard his right to determine when and how and to whom it will be distributed.
Courts who fail to act in such cases are making authors, composers, lyricists and directors “fair game” to piracy and rip-offs.
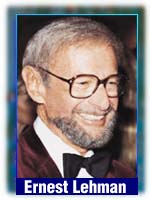
"As much as I approve all advances in technology” said Ernest Lehman, former President of the Writers Guild of America-West, “I’m scared stiff that very soon anything that is written and anything that is filmed could just be stolen anywhere in the world.”
Lehman, whose screenwriting credits include “The Sound of Music” “West Side Story” and “North by North West” said that “unless there is a change in this trend, whole films could be pirated and put on the Internet without any legal recourse for the owner.”
Even such empty philosophical inanities as “nobody really owns anything” and “information wants to be free” breed confusion on the information superhighway. As Winn Schwartau puts it, “The ‘information wants to be free’ cliche makes a great sound bite, but it really means nothing. Information has no persona. And lots of information can — and does — belong to people.”
Free speech is not threatened by copyright law, and neither is the Internet. On the contrary, free speech is threatened by “free theft.” Free speech is abused when it is claimed as a shield to avoid responsibility for unlawful acts.
 The solution is to raise ethical standards through peer pressure from those who live and work in cyberspace. The Church of Scientology contributes to this in numerous ways, including sponsoring the Task Force for Responsibility and Freedom on the Internet, and taking part in the recent roundtable entitled “The Internet and Property Rights” which it helped organize. (See “Solutions in Cyberspace”.) The Task Force broadly distributes a “Netsurfer’s Simple Guide to copyright.”
The solution is to raise ethical standards through peer pressure from those who live and work in cyberspace. The Church of Scientology contributes to this in numerous ways, including sponsoring the Task Force for Responsibility and Freedom on the Internet, and taking part in the recent roundtable entitled “The Internet and Property Rights” which it helped organize. (See “Solutions in Cyberspace”.) The Task Force broadly distributes a “Netsurfer’s Simple Guide to copyright.”
“If the Internet is to flourish” said Mark Rost, head of the Silicon Valley chapter of the Task Force, “the creators of the information on our information superhighway must be protected. Intellectual property rights must be respected. If First Amendment rights are used as a justification for violating property rights, the next step will be the loss of some or all of these rights, as government bodies move in.”

